Estonian eID cryptography mess – 750000 cards compromised
In 2017, a flaw causing vulnerabilities in millions of encryption keys, including national Estonian electronic ID (eID) cards, was discovered. A month and a half after the discovery, the Estonian Police publicly announced the vulnerability, but stated that the eID cards “are completely secure”.
What is public key cryptography?
Firstly, the issue is about public key cryptography. Using public key cryptography, a message is encrypted and decrypted. This encryption relies on a public key and a matching private key. The sender of a message gets the recipient’s public key. The sender uses the public key to encrypt the message and then sends it. The recipient then decrypts the message using the private key that matches the public key that was used to encrypt the message.
In eID systems, the private key is the eID. The private key is used by encrypting a unique numerical representation of a digital file, a checksum, of any document that is to be signed. This checksum proves the authenticity and the integrity to a recipient of such a cryptographically signed document. The encrypted checksum is often called a certificate. This would also be the basis for voting using electronic voting systems.
So, what could go wrong? Well, if there is a vulnerability that allows the public key to be used to create the corresponding private key, anyone can create certificates of documents in someone else’s name, and the system is fundamentally compromised. This increases the risk of ID theft, the manipulation of elections and any other government system that relies on eID.
What happened in Estonia?
In 2014, an independent report found that Estonia’s e-voting system was vulnerable due to its security architecture being based on an obsolete threat model. There were “abundant lapses in operational security and procedures” including “numerous lapses in the most basic security practices” and that the voting system itself had severe vulnerabilities. The report recommended the withdrawal of e-voting.
Now, in 2017, it was discovered that a flaw in a widely used code library has caused vulnerabilities in millions of encryption keys, including national ID cards. These included the electronic ID systems of Estonia and Slovakia. In October 2017, a month and a half after being privately informed of the vulnerability, the Estonian Police announced that that a “vulnerability potentially affecting digital use of Estonian ID cards” had been identified. However, they added, the ID cards “are completely secure”.
The Estonians subsequently backed away from this position and the certificates associated with the 750 000 affected ID cards were suspended. The cards are now being updated with new credentials.
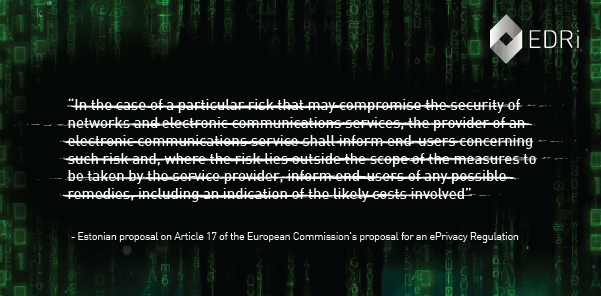
Coincidentally, two weeks after being notified of the vulnerability, the Estonian Presidency of the Council of the European Union circulated a draft “compromise” on the proposal for an e-Privacy Regulation. It included the suggestion to delete Article 17 of the Commission’s proposal on “information about detected security risks”:
“In the case of a particular risk that may compromise the security of networks and electronic communications services, the provider of an electronic communications service shall inform end-users concerning such risk and, where the risk lies outside the scope of the measures to be taken by the service provider, inform end-users of any possible remedies, including an indication of the likely costs involved”.
It could be argued that Estonia has provided a huge service to the European Union. As a small EU Member State, and as current holder of the rotating Presidency of the Council of the European Union, it has, at its own cost, shown the other Member States the huge security issues around sensitive e-government projects. With countries like Ireland launching both a new national ID card system (which is “mandatory but not compulsory“) and planning yet another e-voting system, it seems unable to learn from its own failures, lessons are there to be learned.
Estonian Police notice (13.11.2017)
https://www.politsei.ee/en/nouanded/isikut-toendavad-dokumendid/id-kaardi-ja-mobiil-id-kasutajale.dot
Digital ID cards now only work with new certificates (03.11.2017)
https://medium.com/e-residency-blog/digital-id-cards-will-only-work-with-new-certificates-from-midnight-tonight-6e4db59658b8
Initial Estonian Police statement: For the user of ID-card and mobile ID (13.11.2017)
https://www.politsei.ee/en/nouanded/isikut-toendavad-dokumendid/id-kaardi-ja-mobiil-id-kasutajale.dot
Estonian Presidency e-Privacy “compromise” (08.09.2017)
http://data.consilium.europa.eu/doc/document/ST-11995-2017-INIT/en/pdf
Millions of high-security crypto keys crippled by newly discovered flaw (16.10.2017)
https://arstechnica.com/information-technology/2017/10/crypto-failure-cripples-millions-of-high-security-keys-750k-estonian-ids/
Independent Report on E-voting in Estonia
https://estoniaevoting.org/findings/summary/
Estonian eID article – additional information (22.11.2017)
https://edri.org/estonian-eid-article-additional-information/
(Contribution by Joe McNamee, EDRi)


