EU’s plans on encryption: What is needed?
On 18 October 2017, the European Commission is expected to publish a Communication on counter-terrorism, which will include some lines on encryption.
What is encryption? Why is it important?
When we send an encrypted message (or store an encrypted document), no one else but the intended recipient can read it using a unique key. So even if someone manages to intercept the message when it’s on its way to the recipient, they will not be able to read its contents without the key – they can only see something that looks like a random set of characters. Encryption ensures the confidentiality of our personal data and company secrets. This is not only essential for our democratic rights and freedoms, but it also promotes trust in our digital infrastructure and communications, which is vital for innovation and economic growth. For example, encryption is essential for securing online banking transactions, and protecting the confidentiality of sources in journalism.
Encryption workarounds needed?
The European Commission has come under pressure from some EU Member States to take actions to address the perceived problem of data not being available to law enforcement authorities, due to encryption. This issue is frequently hyped as a major problem, and certain politicians have suggested simplistic and counter-productive policies to weaken encryption as a “solution” to them.
There are several techniques that law enforcement authorities use to access encrypted data. One approach consists in obtaining the key to decrypt the data, for instance, through a physical search when the key is saved on a USB drive. The key can also be obtained from the user directly, for example via social engineering or legal obligation. Another approach is to access the decrypted data through bypassing the key by exploiting a flaw or weakness in the system or by installing software or spyware. However, the existence of workarounds does not mean that law enforcement should resort to them nor that they would be necessary or proportionate, or even compatible with human rights law.
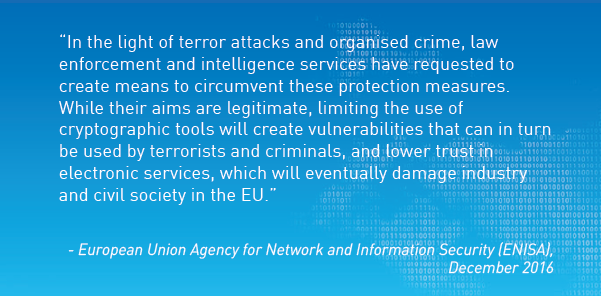
From a technical point of view, encryption cannot be weakened “just a little”, without potentially introducing additional vulnerabilities, even if unintentionally. When there is a vulnerability, anyone can take advantage of it, not just the police or intelligence services. Sooner or later, a secret vulnerability will be exploited by a malicious user, perhaps the same one it was meant to be safeguarding us from. Law enforcement aims are legitimate. However, as pointed out by the European Union Agency for Network and Information Security (ENISA), limiting the use of encryption will create vulnerabilities, lower trust in the economy and damage civil society and industry alike.
What should the European Union do?
A more balanced approach is needed, which avoids much of the rhetoric that is often heard in relation to encryption. Such an approach would recognise a variety of options for addressing this issue without compromising everybody’s security or violating human rights.
Saying “no” to backdoors is a step into the right direction, but not the end of the debate, as there are still many ways to weaken encryption. The answer to security problems like those created by terrorism cannot be the creation of security risks. On the contrary, the EU should focus on stimulating the development and the use of high-grade standards for encryption, and not in any way undermine the development, production or use of high-grade encryption.
We are concerned by the potential inclusion of certain aspects of the forthcoming Communication, such as the increase of capabilities of Europol and what this may entail, and references to removal of allegedly “terrorist” content without accountability in line with the Commission’s recent Communication on tackling illegal content online. We remain vigilant regarding the developments in the field of counter-terrorism.
Read more:
Encryption – debunking the myths (03.05.2017)
https://edri.org/encryption-debunking-myths/
EDRi delivers paper on encryption workarounds and human rights (20.09.2017)
https://edri.org/edri-paper-encryption-workarounds/
EDRi position paper on encryption (25.01.2016)
https://edri.org/wp-content/uploads/2020/10/20160125-edri-crypto-position-paper.pdf
How the internet works (23.01.2012, available in six languages)
https://edri.org/files/2012EDRiPapers/how_the_internet_works.pdf